Personal Note
This week's newsletter is, at its core, about heroes forged in extraordinary circumstances. A colonel alone in the mountains of Iran, hunted and injured but unbroken. Four astronauts venturing farther from Earth than any humans in history, disappearing behind the Moon in radio silence. And somewhere, a kid watching a launch for the first time, feeling the pull of something greater than themselves. The technology stories bookending these accounts, from orbital data centers to AI-generated cinema, are ultimately about the same thing: what humans build when they refuse to accept the limits of what's possible. Welcome to this week's edition of Spies, Lies & Cybercrime!
Title Story: The Moonshot - A childhood dream, a life-changing pivot, and humanity’s bold return to deep space collide in the high-stakes race to claim the Moon’s future.
Security Story of the Week: Rescue in Enemy Territory - A downed U.S. airman survives a relentless manhunt in Iran as intelligence, deception, and cutting-edge technology converge in a daring extraction.
Cybersecurity Breach of the Week: The Director’s Inbox - Hackers breach the FBI Director’s personal email, exposing a harsh truth about how even the highest targets fall through the simplest cracks.
Cybersecurity Tip of the Week: Secure Your Email Now! Four critical steps to lock down your email and eliminate the most common attack paths used by cybercriminals.
AI Trend Of the Week: A hyper-realistic AI-generated rescue blurs the line between storytelling and reality, putting Hollywood-level war narratives in anyone’s hands.
Appearance of the Week: I join Sidecar Sync to share the Hanssen spy case and what it reveals about today’s AI-driven cyber threats—and how to defend against them.
Title Story
The Moonshot

I still remember the first time I saw a space shuttle launch.
I was young—old enough to recognize I was watching something extraordinary, but young enough to believe the world was still wide open. The countdown rolled with a quiet tension that made the crowd fall still. Then ignition. A deep, physical roar you didn't just hear, but felt. The shuttle strained against gravity, rising slowly at first, almost reluctantly, before accelerating into something fierce and unstoppable.
In that moment, my trajectory felt obvious. I was going to be an astronaut.

The Path That Wasn't
Like most kids with a dream that big, I followed the script. I studied hard, stayed disciplined, and earned my way into the Aerospace Engineering program at Auburn University That milestone that confirmed that I was exactly where I was supposed to be.

Then, about a year in, I realized something that didn't fit the narrative I'd built: aerospace engineering wasn't for me. There was no dramatic failure or internal collapse. Just a growing clarity that I was on the wrong path. So I changed majors.
That decision changed everything.
It redirected my life toward the FBI, into counterintelligence, and ultimately into a career spent tracking deception, and, on one occasion, helping bring down one of the most damaging spies in American history. None of that was part of the original plan. But the most important decisions rarely announce themselves. They just nudge you toward a new destiny.
A Course Correction for Humanity
Which is why the Artemis II mission feels strangely familiar.
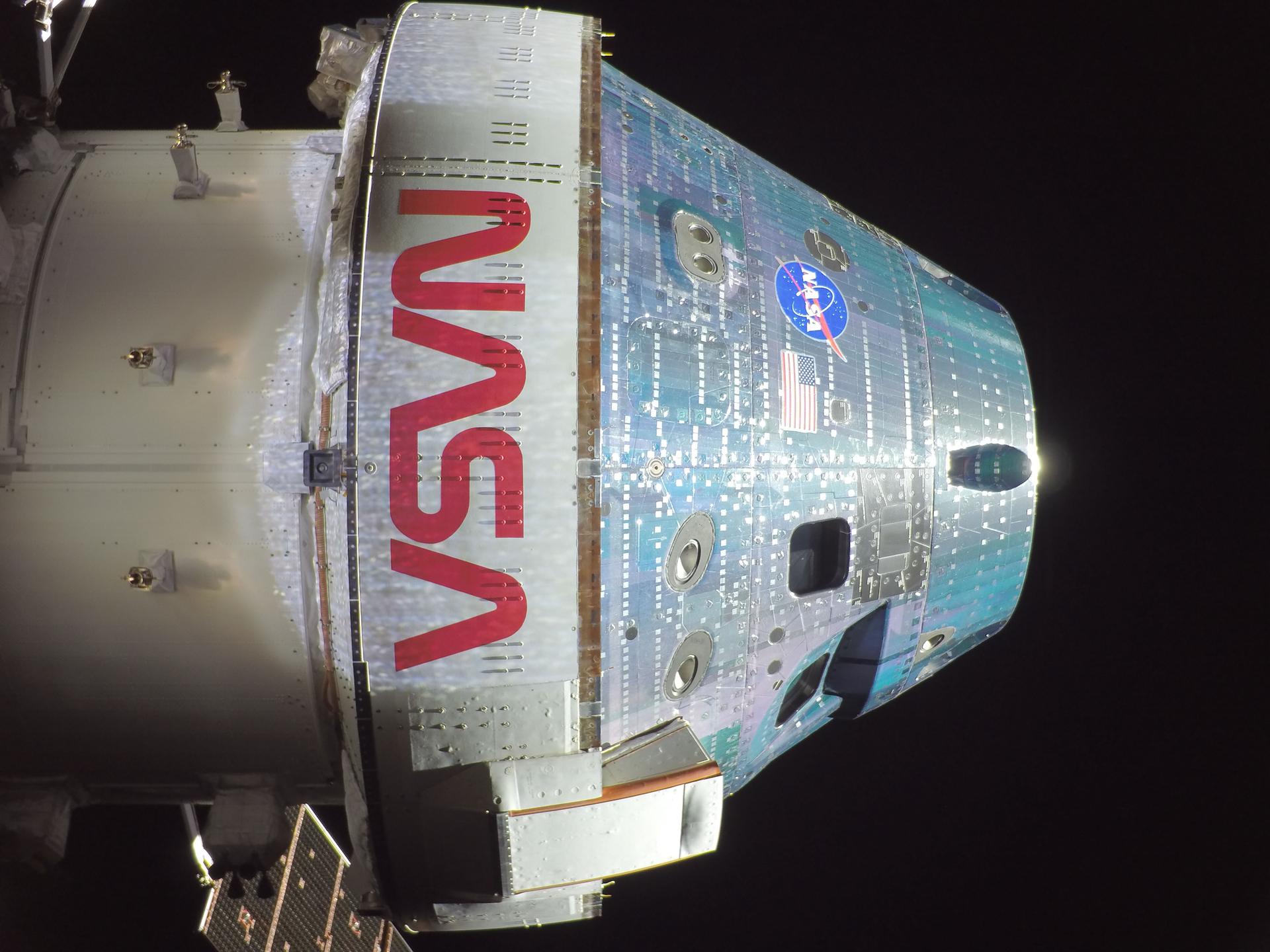
When the Artemis II crew lifted off, they weren't retracing the Apollo path, they were extending it. Christina Koch, Victor Glover, Reid Wiseman, and Canadian astronaut Jeremy Hansen traveled farther from Earth than any humans in history, pushing beyond distances reached by Apollo more than half a century ago. At over 250,000 miles from home, the margin for error narrows to nearly nothing.

Into the Silence
Then there was the far side of the Moon.
For roughly seven hours, the crew disappeared from Earth's reach and passed into a region where communication isn't possible. No live updates. No voice from mission control. Just four astronauts, a spacecraft, and the vast, silent expanse of space. In an era defined by constant connectivity, Artemis II deliberately stepped into isolation, and mastered that new condition.


Beyond Apollo
This is not the space program of the past. Artemis is something more ambitious: the opening move in a sustained effort to establish a permanent human presence beyond Earth.
Apollo proved we could reach the Moon. Artemis is designed to ensure we never have to start from scratch again.

Future missions build on this foundation. Artemis III aims to return humans to the lunar surface, targeting the Moon's south pole. Artemis IV goes further, beginning construction of the Gateway: a lunar-orbiting space station that will serve as a staging point for deeper missions into the solar system.
The New Space Race
But this time, we're not alone.
China has publicly committed to landing astronauts on the Moon by 2030, with a focus on many of the same regions central to NASA's plans. This isn't a Cold War replay, but it is unmistakably a competition—and the stakes are different now.

Source: Popular Science Magazine
The Moon's south pole holds ice trapped in permanently shadowed craters. Water means life support. It also means fuel. Hydrogen and oxygen can power missions far beyond lunar orbit, turning the Moon into a refueling station for deeper space exploration. The first nation to establish a lasting presence there gains more than prestige. It gains leverage.
Control of the High Ground
The implications stretch beyond science. Infrastructure on the Moon will support communications, navigation, and capabilities that could reshape the balance of power here on Earth. Space is becoming contested terrain, and the conversations we're having about AI and cyber dominance may soon share the stage with something even more consequential: control of the space domain itself.
From launch to splashdown, Artemis II demonstrated that the system works. That may sound understated, but in spaceflight, reliability is the foundation on which everything else is built.
The Next Generation
Somewhere, a kid is watching one of these launches for the first time, feeling that same pull I did all those years ago. For many of them, Artemis will be the starting point. A reason to pursue engineering, science, and the difficult and uncertain work of building the future.

Children watching the Artemis II launch. Source: Smithsonian Magazine.
Hopefully, they stay the course.
But if a few of them pivot into something unexpected—if they end up hunting spies instead of exploring space—well, history suggests that might turn out just fine.
Security Story of the Week
Rescue In Enemy Territory
For more than 24 hours, one man was alone in the mountains of Iran.
His F-15E had been shot down deep inside Iranian territory. The pilot was recovered quickly. The second airman, a highly respected U.S. Air Force colonel, was not. He landed miles away, separated, injured, and surrounded by hundreds of Iranian Revolutionary Guard Corps forces fanning across the terrain.
Trained to Disappear
What happened next is the story of incredible tradecraft.
Drawing on Survival, Evasion, Resistance, and Escape (SERE) training, the colonel moved immediately and deliberately. He climbed, scaling a 7,000-foot ridgeline to put distance and elevation between himself and the expanding search perimeter. He found a crevice in the rock and went still, reducing himself to a shadow hiding from the closing net of the enemy.
The IRGC wasn't guessing. They knew roughly where he was and there is evidence that a US spy gave away the colonel’s position. They mobilized ground forces, offered cash incentives to local civilians, and began tightening the net. Videos surfaced of search parties combing the region, turning the hunt into something close to a manhunt with a bounty attached.

Source: The New York Post
The Deception Campaign
While the colonel evaded on the ground, U.S. intelligence launched its own operation— one that would become one of the most complex personnel recovery missions in recent memory.
The CIA's first move was misdirection. They seeded false information inside Iran claiming both airmen had already been recovered. A classic deception play: shift the enemy's focus, create hesitation, buy time. It worked well enough to keep the search from consolidating around the colonel's actual position.
But the harder problem was confirming exactly where he was.
Finding a Heartbeat
That's where the technology became extraordinary.
Using a system known as Ghost Murmur, intelligence operators detected and isolated the faint biological signal of a single human heartbeat. Not a radio call. Not a flare. A heartbeat, identified in hostile terrain, amid noise, movement, and competing signals.
It sounds like science fiction. It isn't. And in this case, it was the difference between a rescue and a capture.
Shaping the Battlefield
Once his position was confirmed, the mission escalated rapidly.
Predator drones began circling overhead, creating an invisible perimeter around the colonel's hiding place. According to a source of mine, any adult male who moved toward that location was treated as a threat and eliminated. It was a calculated, aggressive use of air power designed to ensure one outcome: no one reached him first.
By the time special operations forces moved in, the battlefield had already been shaped by intelligence and technology working in concert.
The Extraction
The recovery itself was anything but clean. Aircraft were damaged. Two MC-130J transport planes malfunctioned after landing and had to be destroyed on the ground to prevent them from falling into enemy hands. Even in success, the operation carried the controlled chaos that defines real-world missions.

But they got him out.
Injured and exhausted, the colonel was extracted from hostile territory — denying Iran the opportunity to capture and weaponize him as a geopolitical bargaining chip.
The operation succeeded not because any single element went perfectly, but because deception, surveillance technology, and precision force were layered together into something the enemy couldn't counter. Each capability bought time for the next one to work.
That's the architecture of modern spycraft. And on this mission, it held.
Cybersecurity Breach of the Week
The Director’s Inbox
The FBI's top man got burned by his Gmail account.
Iran-linked hackers broke into the personal email inbox of FBI Director Kash Patel, rifling through his correspondence and plastering the contents across the internet — personal photos, private documents, and what appears to be his CV.
The operation belongs to Handala, a pro-Iranian hacktivist group that has been running increasingly aggressive campaigns. The leaked material includes personal photographs alongside a mix of correspondence dating between 2010 and 2019. Reporters confirmed authenticity by verifying message headers—the digital equivalent of matching a fingerprint to a file.
The motive isn't hard to read. Earlier this month, the DOJ seized and dismantled four websites linked to Handala. The Patel leak followed shortly after, likely in retribution. The group has also claimed recent hits on Stryker and Lockheed Martin, including wiping thousands of employee devices in what amounted to a scorched-earth data operation.
The FBI confirmed that the breach of Patel’s gmail was limited and no classified or government systems were compromised. But that framing misses the point. Patel was already on Handala's radar. Iranian hackers targeted his personal accounts as far back as December 2024, before he was even appointed director.
This proves my point that anticipating an attack and taking active steps to protect your security is far better than having your personal images blasted across the Internet.
Cybersecurity Tip of the Week
Secure Your Email Now!
Don’t end up like the FBI Director. Here are four steps that close the most common entry points for attackers to compromise your email:
Enable multi-factor authentication (MFA) on every account — use an authenticator app, not SMS, which can be intercepted
Use a strong, unique password that exists nowhere else in your digital life
Audit your account recovery options — backup emails and phone numbers are classic exploitation vectors
Review third-party app access and revoke anything unrecognized or dormant
In the intelligence world, the easiest target is the one that didn't think it was a target at all.
Are you PROTECTED?
My new hub, PROTECT, is now live at ericoneill.net/protect and it’s built for anyone who wants to stop cybercriminal scammers cold. And it’s FREE!
If you want the full battle manual, that’s in Spies, Lies and Cybercrime. If you want to start protecting yourself right now? Begin here
Praemonitus Praemunitus!
Get the Book: Spies, Lies, and Cybercrime
If you haven’t already, please buy SPIES, LIES, AND CYBERCRIME. If you already have, thank you, and please consider gifting some to friends and colleagues. It’s the perfect gift for tech enthusiasts, entrepreneurs, elders, teenagers, and everyone in between.
📖 Support my local bookstore. Get a Signed copy
🎤 I’m on the road doing speaking events. If your company or organization is interested in bringing me to a stage in 2026, book me to speak at your next event.
If you’ve ever paused at an email, login alert, or message and thought, “Could this happen to me?”—my Linkedin Learning course is for you! Login and start learning here.
AI Trend of the Week
This is not a movie trailer. But it feels like one.
A 72-second AI-generated cinematic — rendered entirely in hyper-realistic Lego — recreates the rescue of an American pilot shot down behind enemy lines in Iran. Wounded. Surrounded. Hunted. And still not left behind. From A-10 close air support to a night extraction under fire, the clip delivers tension, emotion, and pacing that used to require a Hollywood budget.
Now it requires a prompt and a render queue.
But the real question lingers after the clip ends: is this entertainment — or the opening frame of something larger? AI just handed the power of war storytelling to anyone with an idea and an internet connection.
Read the full rescue story in this week's Security Story — the real operation is every bit as cinematic as the Lego version.
Appearance of the Week
This week, I sit down with Mallory on Sidecar Sync to share the inside story of the operation that led to the capture of FBI spy Robert Hanssen—and what it reveals about today’s cyber threats. We dive into how cybercriminals really operate, why smaller organizations are easy targets, and how AI is accelerating deception. I also break down practical steps you can take right now to protect your people, data, and trust.
Please support my sponsors. It only takes a click - no purchase necessary!
The Gold Standard for AI News
AI keeps coming up at work, but you still don't get it?
That's exactly why 1M+ professionals working at Google, Meta, and OpenAI read Superhuman AI daily.
Here's what you get:
Daily AI news that matters for your career - Filtered from 1000s of sources so you know what affects your industry.
Step-by-step tutorials you can use immediately - Real prompts and workflows that solve actual business problems.
New AI tools tested and reviewed - We try everything to deliver tools that drive real results.
All in just 3 minutes a day
Like What You're Reading?
Don’t miss a newsletter! Subscribe to Spies, Lies & Cybercrime for our top espionage, cybercrime and security stories delivered right to your inbox. Always weekly, never intrusive, totally secure.
Stay safe out there!
~ Eric