Personal Note:
Fellow Spy Hunters:
Some of you noticed—no newsletter last week. That one’s on me.
I wrote it on the road, squeezed between keynotes, meetings, and media hits. It was one of those weeks where everything moves fast…until something important slips. In the middle of that controlled chaos, I missed hitting “publish” at 9:03 AM EST on Tuesday. Not exactly a small detail.
There’s no shortage of stories right now. I was tempted to pack this issue with everything—from the awe of the Artemis mission to rising tensions with Iran, to the very real threats against critical infrastructure, and the nonstop barrage of cyber scams filling our inboxes. But cramming it all in would do more harm than good.
Artemis II deserves its own spotlight. Watching it break through our atmosphere and head toward the moon was something special. I’ll give that story the attention it deserves next week.
Today, we focus on Iran—and an exceptional spy story you won’t want to miss.
Enjoy the issue. Let me know what you think. And as always, stay safe out there.
—Eric
Title Story: From Hanssen’s dead drop to Silicon Valley insiders, the evolution of espionage proves the most dangerous threat still comes from within.
Cybersecurity Breach of the Week: Iran isn’t hacking hospitals—they’re hitting the lifelines behind them, using proxy cyber crews to quietly disrupt the systems that keep modern infrastructure alive.
Cybersecurity News of the Week: The timeline for quantum computing just accelerated, putting today’s encrypted secrets on a rapidly ticking clock.
Technology Trend of the Week: Meta’s courtroom loss raises a hard question—what happens when platforms know the harm and let it happen anyway?
AI Trend Of the Week: As AI becomes the front door to information, we may be outsourcing more than answers—we may be outsourcing curiosity itself.
Appearance of the Week: A national TV breakdown of Iranian espionage brings the hidden threat of insider spies into the public spotlight.
Title Story
The Spy Sisters: From Dead Drops to Firewalls
It was cold the night Robert Hanssen walked onto the footbridge. If you've ever been out to Foxstone Park in Vienna, Virginia, you know the kind of cold that settles into your bones, quiet and still, the kind of night where every footstep sounds louder than it should.
Hanssen preferred it that way. Fewer variables. Fewer witnesses.
He carried a small package containing real names, real methods, real operations. Lives he compressed onto media that could fit in your hand and destroy a country's advantage in an instant. He moved with purpose but without urgency, because that's the difference between amateurs and professionals. At the base of the footbridge, he made his drop, a simple physical transfer from one human to another, separated by time and space but connected by intent. Minutes later, he was gone. It worked, until a source betrayed him and my undercover investigation caught him.
Now fast forward.
No bridges. No frozen parks. No chalk marks or dead drops hidden under wooden planks. Instead, imagine two sisters sitting in a well-lit Silicon Valley office. Badge access. Legitimate credentials. Trusted roles. Their keyboards quiet. Their behavior unremarkable. Their access entirely authorized.
Samaneh Ghandali, 41, and her sister Soroor, 32, were engineers based in San Jose who had secured positions at some of the most sensitive technology companies in the world, including Google, where Samaneh worked as a hardware engineer and Soroor as an intern. Their brother-in-law, Mohammad Khosravi, a former member of Iran's military, was employed at a separate tech firm. Their father, Shahabeddin Ghandali, is a regime insider in Iran who once served as chief executive of the Teachers Investment Fund Corporation and was arrested in 2016 on embezzlement charges totaling $2.5 billion. I doubt the family ties are a coincidence.

Inside the companies' systems, the trio moved freely. They weren't breaking in, they were already inside. Prosecutors allege the defendants transferred more than 300 files, including trade secrets related to processor security and cryptography, to unauthorized third-party platforms, personal devices, and work devices belonging to each other's employers, with some of that data ultimately transferred to Iran.
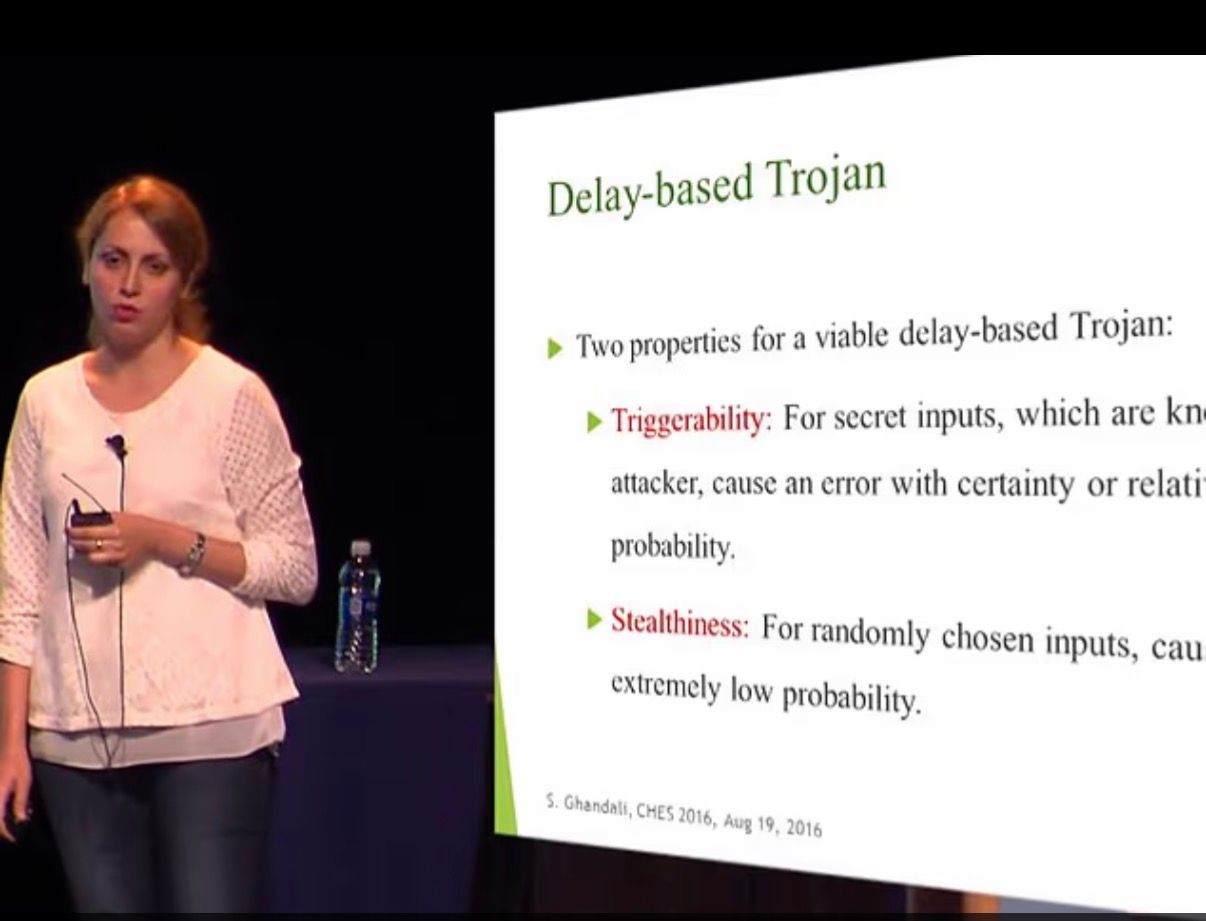
Then security tightened. The sisters adapted. After Google flagged Samaneh Ghandali's activity and restricted her access in August 2023, she signed an affidavit saying she had not shared confidential information outside the company. Then, the night before she and Khosravi traveled to Iran in December 2023, she allegedly photographed approximately 24 screens of restricted data from her husband's work computer. No more downloads. No more obvious transfers. Just a phone and a camera--crude, but invisible to any system log.
Hanssen needed a bridge. They just needed a camera.
This is the part most people get wrong about espionage. We like to believe it's about technology like firewalls, zero-day exploits, and nation-state hacking units hammering away at our digital defenses. That's the Hollywood version. The reality is far less dramatic and far more dangerous, because the most effective attack doesn't break in. It logs in.
The alleged activity in the Ghandali case reads like a patient, disciplined intelligence operation. Access wasn't forced; it was earned, maintained, and exploited over time. When pressure increased, tactics shifted. When confronted, denial followed.
Their tradecraft fits a pattern that intelligence professionals have been watching for years.
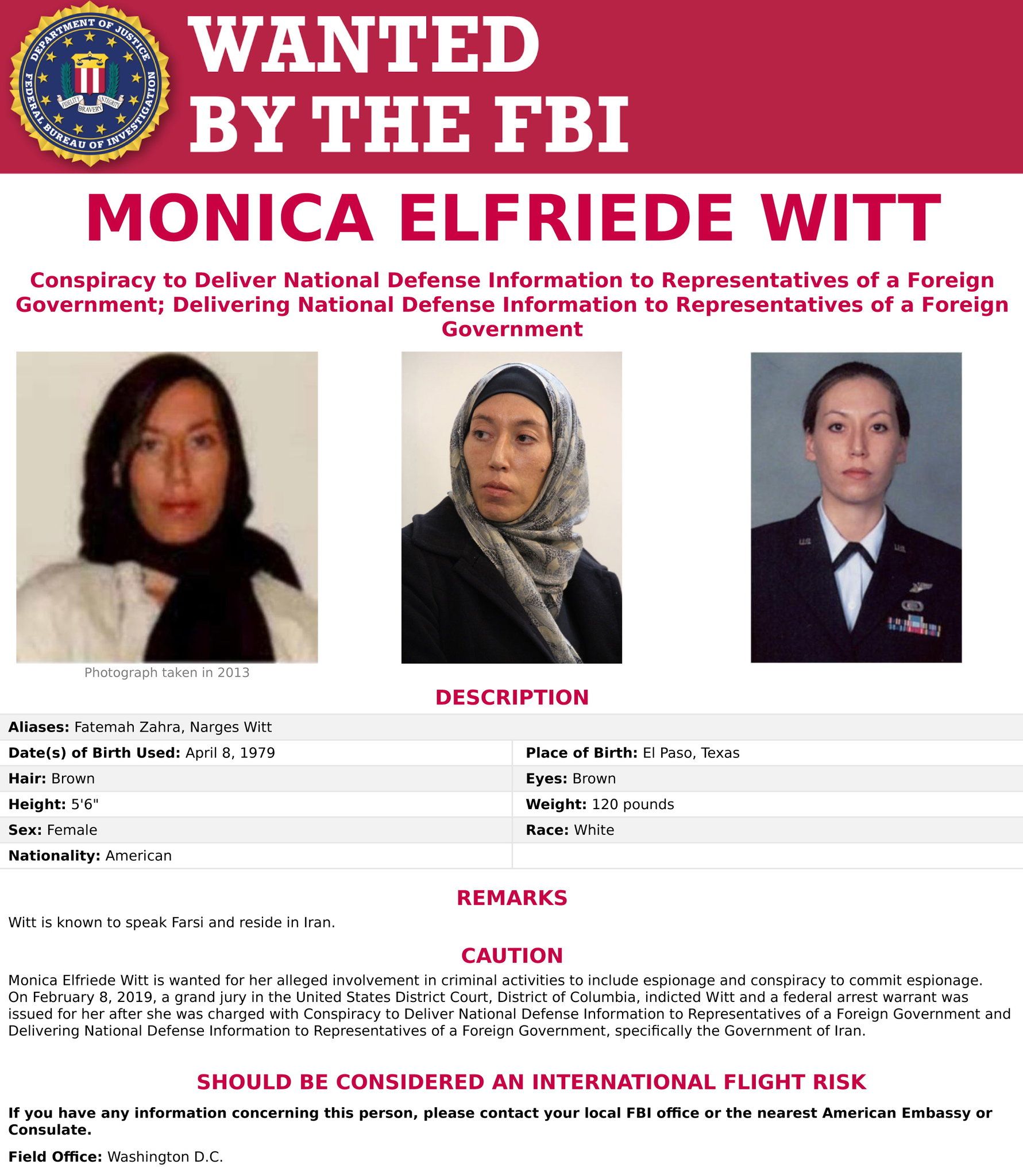
Monica Witt was a former Air Force technical sergeant and counterintelligence special agent who defected to Iran in 2013 carrying years of U.S. operational knowledge in her head. She didn't hack her way into anything. After arriving in Tehran, she constructed detailed dossiers on former U.S. government agents and disclosed the classified identity of at least one serving intelligence officer, placing that person's life at direct risk. She remains a fugitive today, believed to be living in Iran.
Niloufar "Nellie" Bahadorifar never touched a classified document in her life. She didn't need to. A California resident originally from Iran, she facilitated flows of money, access, and influence, quietly and persistently, in service of an Iranian government plot to silence a dissident journalist living in New York City. She even paid a private investigator to conduct surveillance of the intended victim! After pleading guilty, Nellie was sentenced to four years in prison.

Again and again, across these cases, the same uncomfortable question surfaces: how close can someone get before we realize what they're doing? The answer is often the same. Too close.
The lesson hasn't changed since that cold night on the footbridge. Hanssen didn't defeat the FBI with superior technology. He undermined it with access, exploiting trust, and patiently relying on time. What has changed today is speed. Today's insiders can move more data in five minutes than Hanssen moved in years, transmit it instantly, hide it in plain sight. The barrier to entry has collapsed. But the core vulnerability remains exactly where it has always been: people.
Your biggest risk isn't the attacker outside your network. It's the person already inside it who decides to stop being on your side. You hunt that threat by understanding behavior and asking the question: who is accessing what, and why, and what doesn't quite fit?
Insider threats don't announce themselves. They reveal themselves slowly and subtly, until one day, if you're paying attention, the pattern becomes clear. And if you're not, you find out the way we did with Hanssen. After the spy succeeds in the worst possible place.
Cybersecurity Breach of the Week

Iran is also attacking critical infrastructure through its cyberattack groups and partners. On March 11, 2026 Iran’s cyber attack group Handala attacked Stryker—a company deeply embedded in the global healthcare supply chain. The disruptive, destructive operation that destroyed data and knocked out Stryker’s Microsoft environment worldwide, delaying shipments and impacting medical services without ever touching a hospital directly.
This is the new playbook: use proxy hacker groups tied to Iran’s intelligence apparatus to strike the systems behind critical infrastructure—healthcare, energy, logistics—creating real-world consequences while maintaining plausible deniability. It’s not about stealing money; it’s about sending a message, applying pressure, and proving that in modern conflict, you don’t need bombs to disrupt a nation. You just need access.
Cybersecurity News of the Week
The Espionage Clock Just Got Shorter
Google dropped a quiet bombshell this week: Q-Day—the moment quantum computers can shatter today's encryption—has been moved from the distant 2040s to as early as 2029. That's a five-alarm fire for every intelligence agency on the planet.
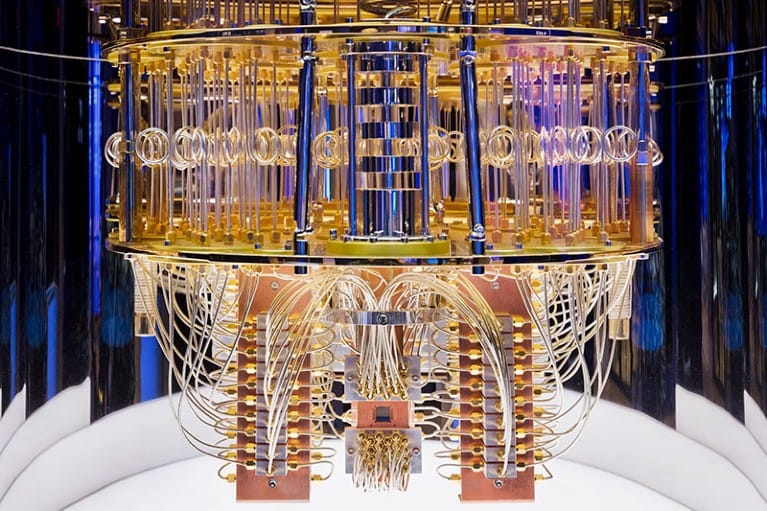
In my book Spies, Lies and Cybercrime, I dedicate an entire chapter to Quantum Supremacy and what it means for the espionage world. The core argument: whichever nation develops a quantum computer at scale first doesn't just win a technology race, they instantly win the intelligence war. Every secret ever encrypted becomes readable overnight.
This is because of a strategy already well underway called "Steal Now, Decrypt Later." Hostile states and criminals have very likely been collecting encrypted communications, messages, emails, and documents for years, sitting on hard drives, waiting for the quantum moment to arrive. Data captured in 2026 and earlier may be compromised years later, regardless of whether systems were "secure" at the time of transmission.
These algorithms currently protect decades of secrets belonging to militaries, banks, governments, and individuals globally. Google is urging a full migration to post-quantum cryptography by 2029. NIST had set 2035 as its target — Google just moved the goalposts six years closer.
Three years. The clock is running.
Get the Book: Spies, Lies, and Cybercrime
If you haven’t already, please buy SPIES, LIES, AND CYBERCRIME. If you already have, thank you, and please consider gifting some to friends and colleagues. It’s the perfect gift for tech enthusiasts, entrepreneurs, elders, teenagers, and everyone in between.
📖 Support my local bookstore. Get a Signed copy
🎤 I’m on the road doing speaking events. If your company or organization is interested in bringing me to a stage in 2026, book me to speak at your next event.
If you’ve ever paused at an email, login alert, or message and thought, “Could this happen to me?”—my Linkedin Learning course is for you! Login and start learning here.
Technology Trend of the Week
Meta's Defense Was Basically "Kids Were Going to Get Hurt Anyway"
A New Mexico jury spent exactly one day deliberating before ordering Meta to pay $375 million in damages, which tells you something about how their defense fizzled.

The verdict, reached March 24, is the first time a U.S. state has beaten Meta in court over child safety. Jurors found the company knowingly harmed children's mental health and concealed what it knew about child sexual exploitation on its platforms. The case stemmed from a 2023 undercover investigation where New Mexico AG Raúl Torrez's office created fake profiles of underage users, which were promptly flooded with sexually explicit material and contacted by adults seeking similar content.
The $375 million is well short of the $2.1 billion the state sought, though jurors awarded the maximum $5,000 per violation under state law. For context, Meta pulled in $201 billion in revenue in 2025. Naturally, the company plans to appeal.
Full disclosure: my wife and I kept our kids off social media entirely, through monitoring, lectures, and what I can only describe as sustained parental stubbornness, until they were old enough to grasp two non-negotiable truths: someone you only know online is not your friend, and nothing you see or hear on social media should be trusted at face value. It wasn't easy. It was worth it.
A second trial phase begins in May, where a judge will decide whether Meta created a public nuisance and should fund programs to address the damage. That one could get pricier.
AI Trend of the Week
ChatGPT Now Knows If It's Raining
AccuWeather has launched a ChatGPT integration so you can ask an AI chatbot whether to bring an umbrella—a problem that the plain, English weather app on your phone was already solving just fine.

To be fair, there's a sliver of utility here. You can now ask ChatGPT things like "Is it a good afternoon for a run?" and get a weather-informed answer rather than a raw forecast you have to interpret yourself. The integration includes AccuWeather's RealFeel and MinuteCast data, displayed in an interactive module.
But it raises a bigger question: are we watching the slow death of the web browser? Of the standalone app? Of Googling something yourself? If every answer to every question, from tomorrow's forecast to your medical symptoms to your legal rights, gets routed through a personal AI Agent, what happens to our instinct to investigate, to discover, to be wrong and then figure out why? There's something quietly profound about the habit of looking things up yourself. Once we outsource that reflex entirely, getting it back may prove harder than checking the weather.
Appearance of the Week
I joined NewsNation and Chris Cuomo to break down the latest Iranian spy case uncovered in the United States. Alongside Tracy Walder, we dig into the investigation and what Iran’s expanding espionage efforts mean for Americans at home.
Please support our sponsors. It only takes a click. No purchase necessary.
The best marketing ideas come from marketers who live it.
That’s what this newsletter delivers.
The Marketing Millennials is a look inside what’s working right now for other marketers. No theory. No fluff. Just real insights and ideas you can actually use—from marketers who’ve been there, done that, and are sharing the playbook.
Every newsletter is written by Daniel Murray, a marketer obsessed with what goes into great marketing. Expect fresh takes, hot topics, and the kind of stuff you’ll want to steal for your next campaign.
Because marketing shouldn’t feel like guesswork. And you shouldn’t have to dig for the good stuff.
Like What You're Reading?
Don’t miss a newsletter! Subscribe to Spies, Lies & Cybercrime for our top espionage, cybercrime and security stories delivered right to your inbox. Always weekly, never intrusive, totally secure.



